We are here to help you through the paperwork process. If at any point you need assistance please feel free to email our Service Center or contact your advisor directly.

Many Internet scams today involve email messages that appear to come from a trusted source, but are not trustworthy. Additionally, email attachments can be harmful because they may contain viruses.
The below can be indications that an email is fake:
Here are some ways to protect yourself from email fraud:
Choosing your password well and keeping it a secret can be key steps to safeguarding all of your online transactions. To create a password that is more difficult to guess, use a combination of letters and numbers for passwords you create, such as “4funcallC3po” or “Il9vemyd1g.” Certain passwords are easier to compromise, so try to avoid common pitfalls by creating secure passwords:
Make sure you only access personal information through websites that use Secure Sockets Layers (SSL). An SSL offers an additional layer of security that many sites use. You can check whether the site you are on has an SSL in effect by checking for two things:
If you get a pop-up message indicating a problem with a site’s Security Certificate, do not proceed. The website should be secured with a digital certificate, which verifies you’re at a legitimate website and not a “spoofed” site.[/fusion_toggle][fusion_toggle title=”Know the Threats” open=”no”]It’s important to be aware of possible risks to your computer and the information on or passing through it. We have a designated team responsible for reviewing potential threats to clients’ assets and information.
Your awareness, combined with our vigilance, can help to decrease the risk to your accounts and information.
Familiarize yourself with the threats posed by:
Identity theft
Identity theft—using a person’s personal or financial data to commit fraud—is one of the most rapidly growing global crimes. The targets of this crime are personal information, financial information, and access to online accounts.
The personal information often targeted includes:
The financial information often sought is:
Phishing happens when someone attempts to steal personal or financial information. It usually starts with an email asking for sensitive information, such as your User ID or user name, your password, or your account information. Phishing—sometimes referred to as pharming—opens the door to identity theft and computer security breaches.
Please note: Trek advisors and staff, and any of their affiliates will never ask you for your account number, User ID, PIN, password, or any other personal information in an email. (In rare cases, however, we might need to ask you for the last four digits of your account number for identification purposes.)
For more details on how you can help protect your investments, log in to AdvisorClient.com and access the Security Center from the Client Services tab on the site menu.
Dreaming up a different password for every site and service is the only way to keep your stuff safe online, but it’s also a gigantic nuisance. There’s one thing you can—and should—do to help: Get a password manager program. The three programs below all will help in lessening your password woes. Please see the break down below and choose one that would work for you.
But, wait—isn’t storing all your passwords in one place a terrible idea? It’s better than reusing easily remembered passwords everywhere. Password managers hide your information behind a master password that only you know.
Nothing is 100% guaranteed, but all three of these managers take the additional security step of never sending your master password over the Internet. They’re like a safe-deposit box that a professional keeps without knowing what’s inside, or even holding a key to open it.
In an age where more of our personal information lives, password protected, up in the cloud, we need defenses beyond antivirus software. Using a password manager is the next step.
These programs are becoming increasingly popular as hackers try to infringe on your personal data through passwords that can be cracked as easily as eggs. Here, I’ve put three of the most popular password managers to the test to help you choose the software that best suits your needs.
Encryption and database
Like 1Password and LastPass, Dashlane uses the AES-256 encryption for its database. The key that encrypts the data is derived from the master password: the decrypted data is not stored on your device or Dashlane’s servers.
Dashlane gives you the possibility to keep encrypted data locally on one device, or to sync it between multiple devices via Dashlane’s servers. The encrypted data is hosted on Dashlane’s servers and is downloaded and decrypted every time.
Just like Lastpass, Dashlane lets you add two-factor authentication options to enhance the security of your master password.
Integration with browsers
Dashlane is compatible with Chrome, Firefox, Internet Explorer, and Safari. The application lets you import your saved passwords in Firefox or another browser.
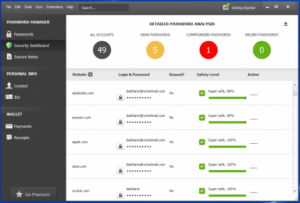
Threat prevention
Dashlane sends security alerts directly to your devices when your passwords could be compromised. Dashlane also advises on the saved passwords.
Platforms
Dashlane is available for: Android | iOS | Mac | Windows
Encryption and database
With Lastpass, all your data is encrypted locally on your PC using AES 256 encryption, and you’re the only one who can unlock it. Your key doesn’t leave your device, and it’s never shared with LastPass.
The only downside is that the program requires an internet connection because the encrypted data is hosted on LastPass servers by default. Fortunately, you can access the data without an internet connection through the LastPass Pocket app.
One good thing is that LastPass supports two-factor authentication. It’s a practical solution to add another layer of security to the master password.
Integration with browsers
LastPass is compatible with the following browsers: Chrome, Dolphin Browser, Firefox, Firefox Mobile, Internet Explorer, Maxthon, Opera, and Safari. The app also imports existing passwords from Firefox and Internet Explorer.
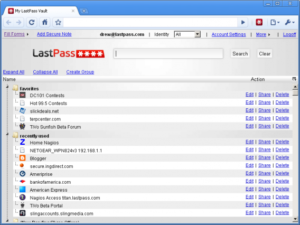
Threat prevention
LastPass offers a line of defense against phishing attacks, and it will not fill in forms hosted on malicious websites. The application also analyzes passwords to find out if they’re weak: LastPass will warn you when you’re using a weak password when logging into your accounts, and it’ll send you security alerts every time a new security breach is discovered.
Platforms
LastPass is available for: Android | BlackBerry| iOS | Linux | Mac | Windows | Windows Phone
Encryption and database
1Password uses AES-256 encryption but stores all your data locally on your computer. Even if you choose to synchronize your data with other devices, your master password, the unique decryption key, never leaves your computer or device. Decryption is always done locally and the decrypted data is never written on the disk.
With 1Password, using the cloud is an option, not a requirement. The software lets you synchronize data between devices via iCloud and Dropbox, or locally through Wifi. It’s an ideal solution for mobile users who are more cautious about the cloud.
Integration with browsers
1Password is compatible with Chrome, Firefox, Opera, and Safari. Extensions allow the app to automatically save new passwords entered in the browser and to automatically fill out forms with just one click.
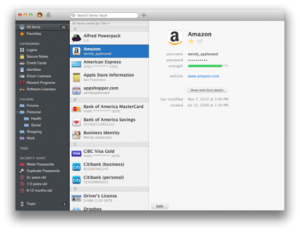
Threat prevention
The Watchtower feature in 1Password identifies sites that are vulnerable to cyber attacks and tells you which passwords you should change. The app will tell you which sites to avoid, and gives you the green light to change your password after covering security holes.
Another good feature is that 1Password will also tell you if your passwords aren’t safe enough, are duplicate, or are obsolete so that you can update them.
Platforms
1Password is available for: Android | iOS | Mac | Windows | Windows Phone
All three password managers are very similar in many ways. On a security level, they all use the AES-256 security standard and store their data locally. In the end, your preference for one or another will boil down to the additional features of each program.
Dashlane’s mobile apps will give an experience (auto-completion, generating passwords) that’s very close to what is offered for PC thanks to a dedicated keyboard on Android and a full browser on iOS.
For LastPass, it’s the unparalleled variety of available platforms what will make the difference. Of the three, this is the only one that supports Linux, BlackBerry, Windows Mobile, Symbian, and Firefox OS, an ideal choice if you’re using one of these platforms. The app, however, syncs your encrypted data on its servers by default, a solution that will discourage those who are most skeptical about cloud security.
1Password is notable for how easy it is to use and its elegant design. If you fear that you’ll end up with something indecipherable, 1Password is a good solution. This is indeed the best password manager for less advanced users, and the function that lets you sync data between devices via Wi-Fi could attract savvy users not wanting their data copied to the cloud.
Approved senders (safe senders) are people and domains you always want to receive email messages from. Safe recipients are recipients that you don’t want to block, usually groups that you’re a member of. Messages received from any email address or domain in your safe senders and recipients list are never sent to your Junk Email folder.
IMPORTANT: The server that hosts your mailbox may have junk email filtering settings that block messages before they reach your mailbox.
1. Sign in to Outlook Web App. For help, see Getting started in Outlook Web App.
2. At the top of the page, select Settings > Mail.
3. Under Options, select Block or allow.
4. To add an entry to Safe senders and recipients, enter the email address or domain that you want to mark as safe in the Enter a sender or domain here text box, and then press Enter or select the Add icon + next to the text box.
5. (Optional) Select the Trust email from my contacts check box to treat email from any address in your contacts folders as safe.
6. Select Save to save your changes.
To add a Safe Sender within your Gmail account, you will need to add a filter to notify the system to allow particular email type or senders to flow through to your inbox.
How to create a filter in Gmail:
Note: When you create a filter to forward messages, only new messages will be affected. Additionally, when someone replies to a message you’ve filtered, the reply will only be filtered if it meets the same search criteria.
How to use a particular message you receive to create a filter:
Adding contacts to your trusted Yahoo sender list is fairly simple as your Contact List is simultaneously your Yahoo email safe sender list.
Open the email sent to you by the contact you wish to label as safe. Be sure to check both the inbox folder and junk or spam folder.
Copy the email address
Click the Contacts icon located in the upper right-hand corner of your Yahoo! Mail Inbox Homepage. When you scroll over the first icon, it should say ‘Contacts’.
Click ‘Add a new contact’ located below the list of your contacts.

Fill in the contact details and paste the email address you wish to add to your contact list.
Click Save.